Reverse engineering CryptoPanic REST API
Dig into JS bundle to find useful stuff
Software engineer based in Singapore
Welcome to my website, where I write mostly on tech-related content to share the things I learned from people and from building projects using different tools.
My interests are in tech, traditional finance, cryptocurrency.
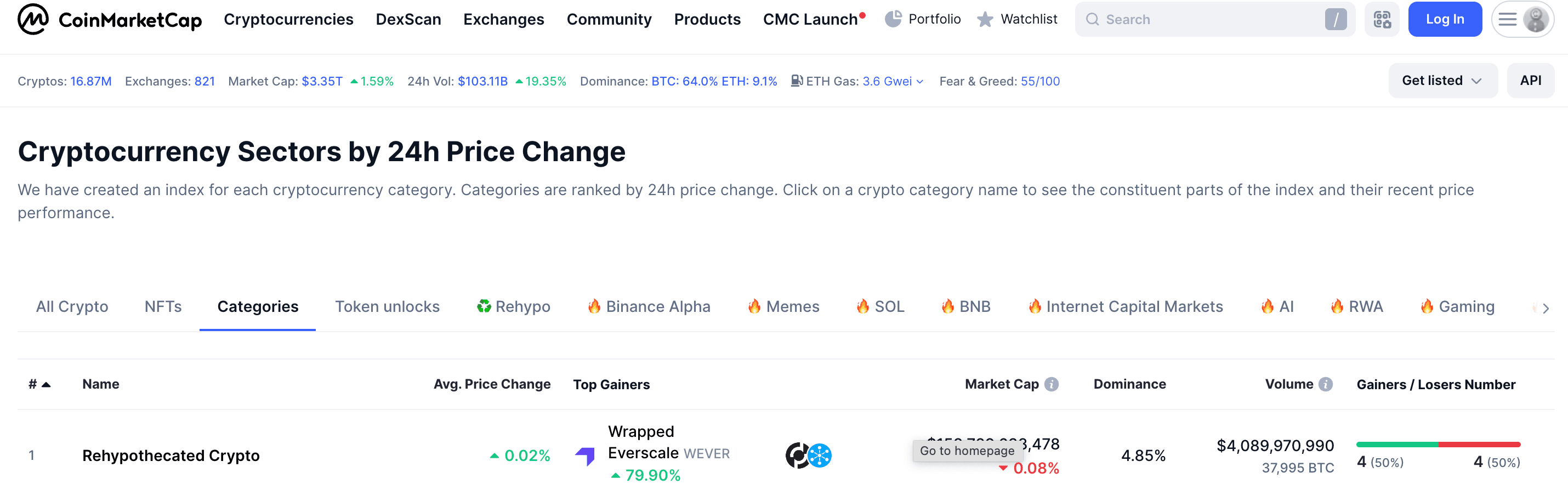
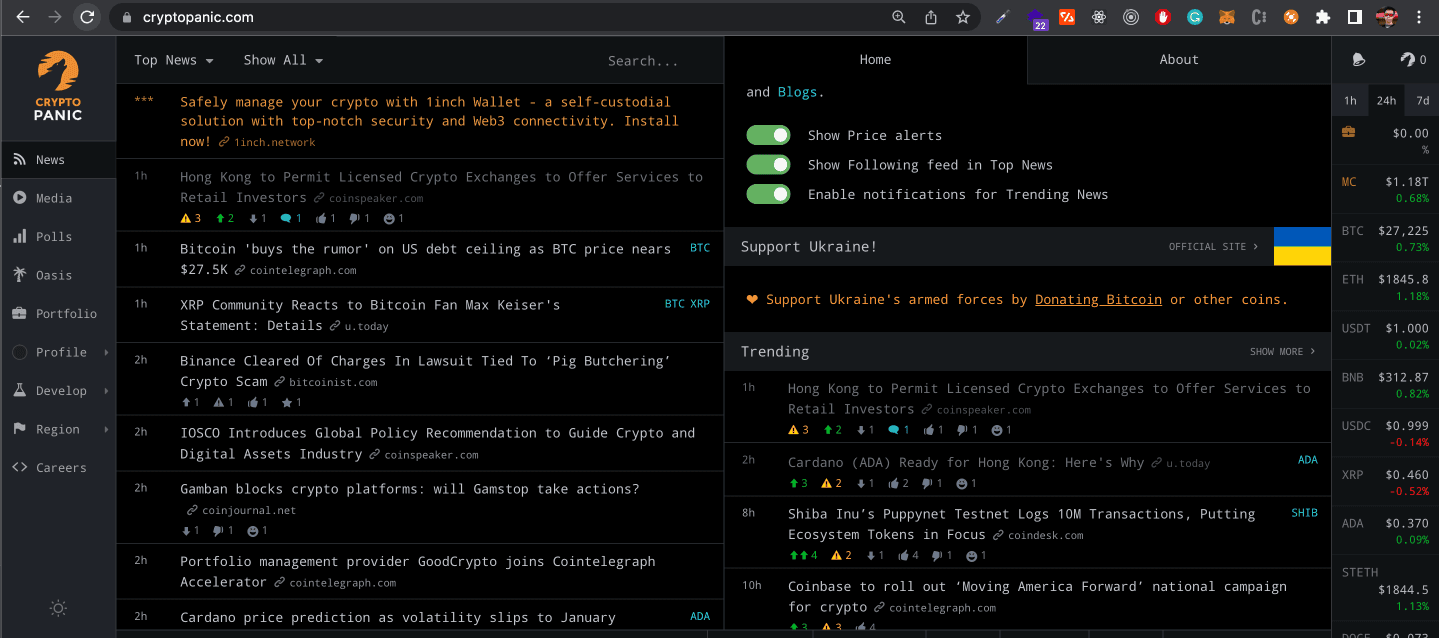
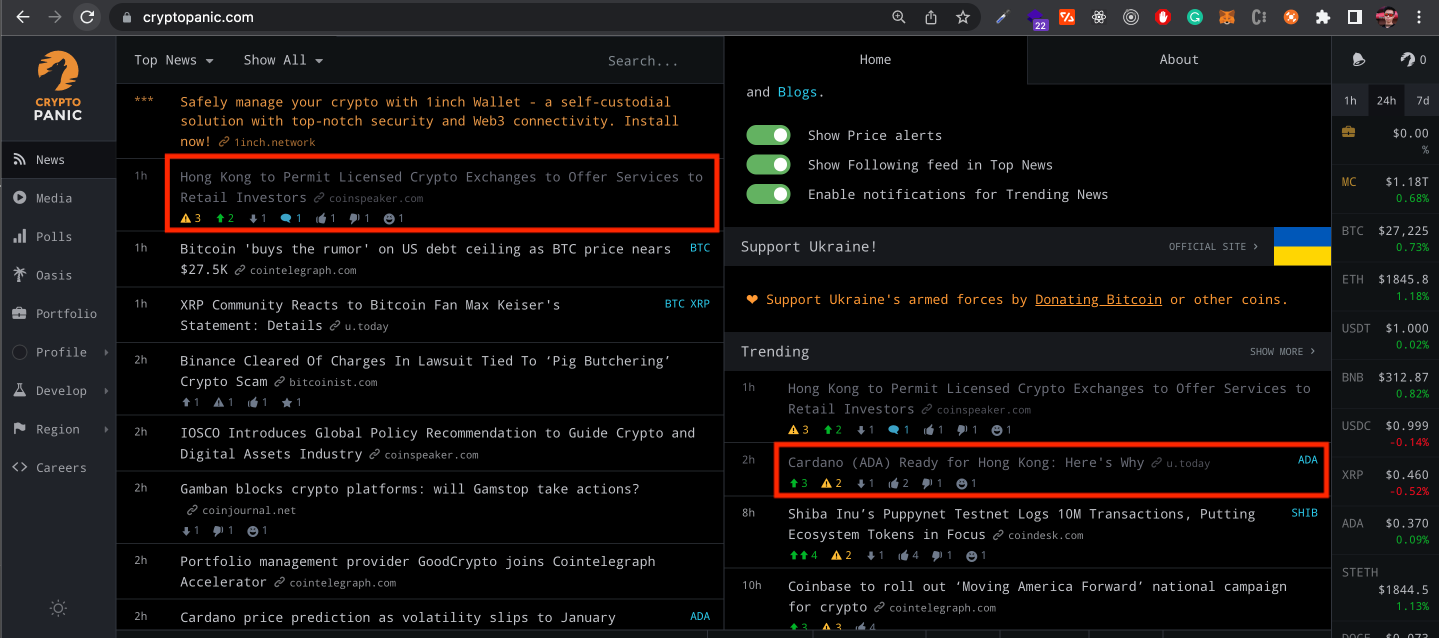
CryptoPanic is a news aggregator website for trending news based on social sentiment. It's a good website for keeping up to date on the latest news, as well as using it as a trading signal.
Its compact layout reminds me of hacker news. I was looking through the network requests and got intrigued after finding out that the main data is not in plaintext:
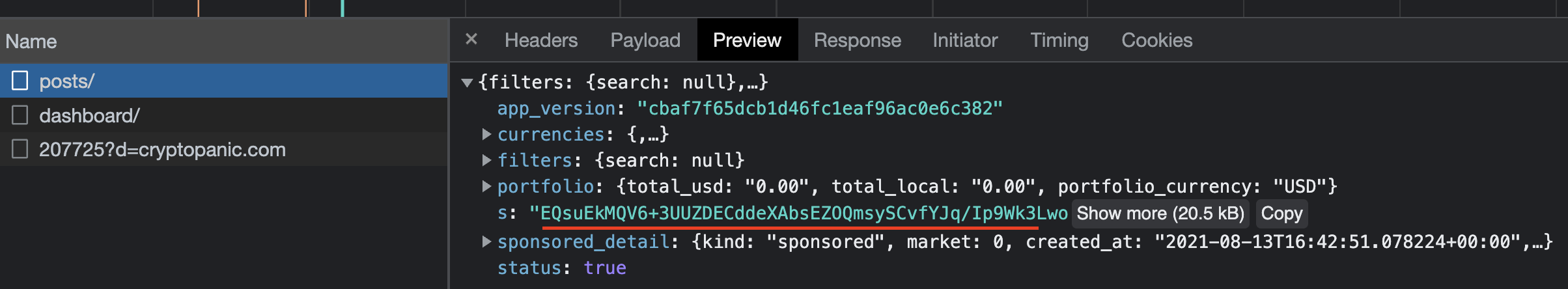
The server sends some sort of encoded data, and the client decodes it. After digging around the js bundle, I manage to recover the plaintext data that is displayed on the website.
Note: This post is for educational purpose only.
The reverse engineering process
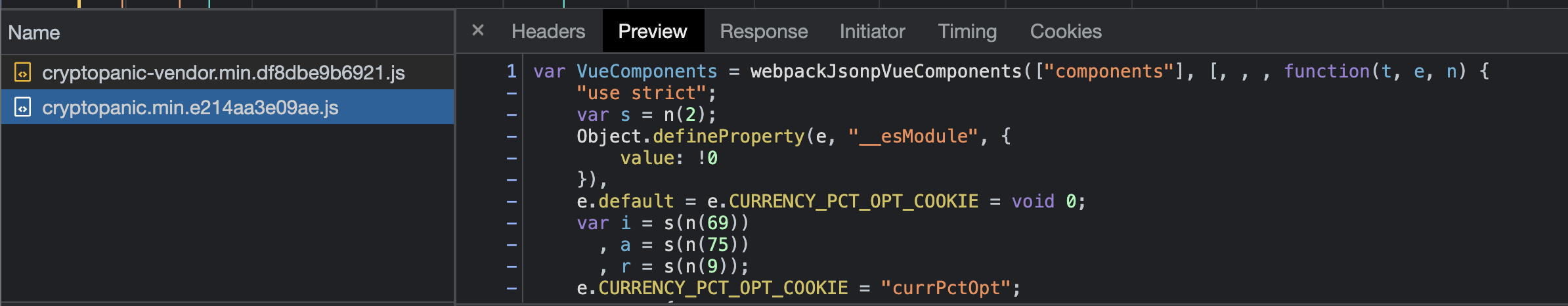
1. Open the js bundle
The first thing is to find out which part of the javascript code is responsible for decoding this response. Begin by searching for and opening the js bundle cryptopanic.min.xxxxx.js.
2. Locate the part of the code that decodes the data
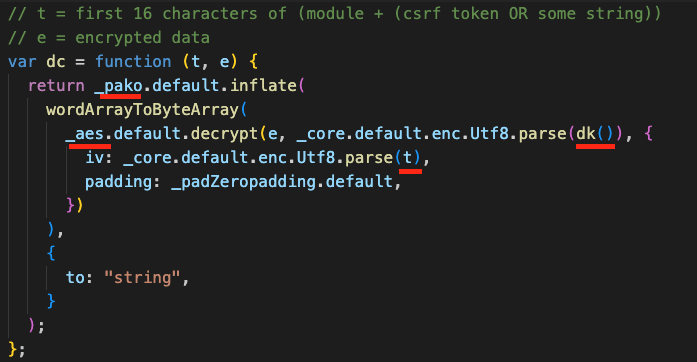
Searching for "decrypt" immediately zooms in on this function called dc that does the core work of decoding the data.
dk() returns the encryption key, together with parameter t which is used as the Initialization Vector(IV), are passed through the AES algorithm with zero padding.
wordArrayToByteArray converts the decrypted response into a byte array, and pako.default.inflate decompresses the data, and converts them into javascript's utf-16.
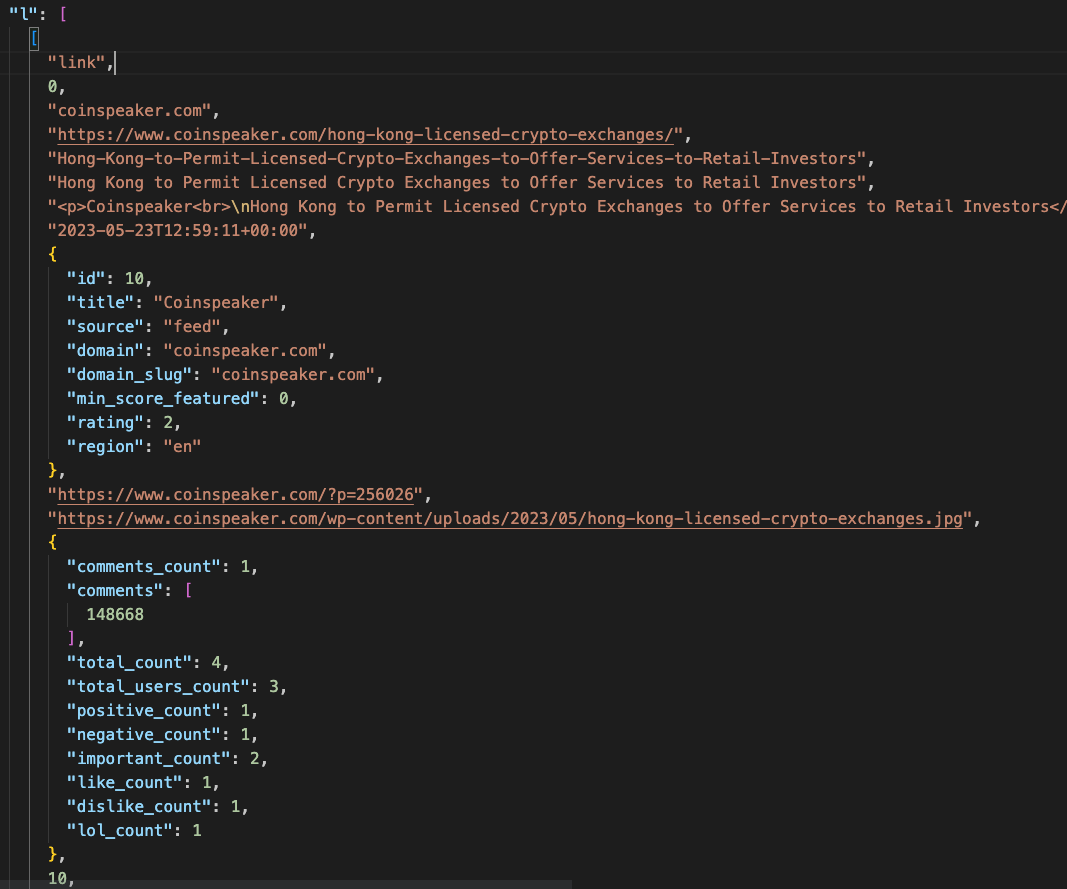
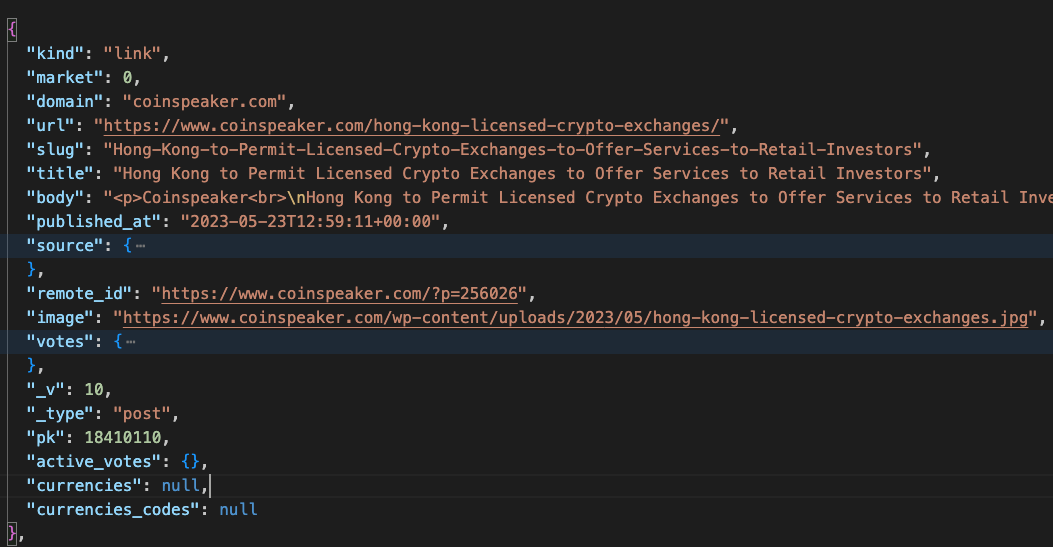
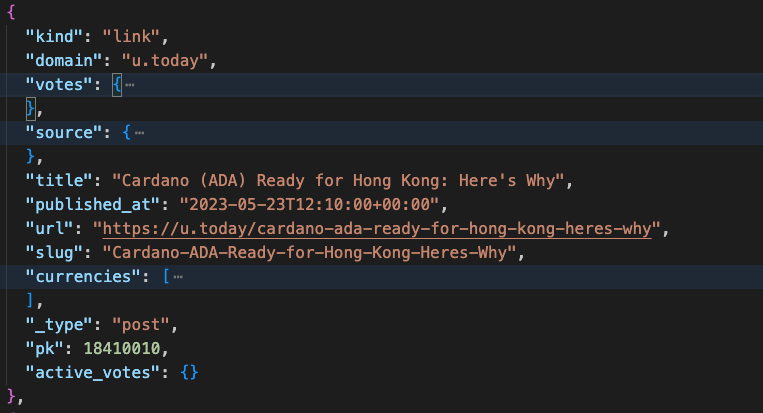
After this step, the result is a JSON string of the API response. The JSON version looks like this:
3. Transform the raw response into a usable array of objects
The last step is to transform the raw JSON into an array of objects so that it is easy to work with.
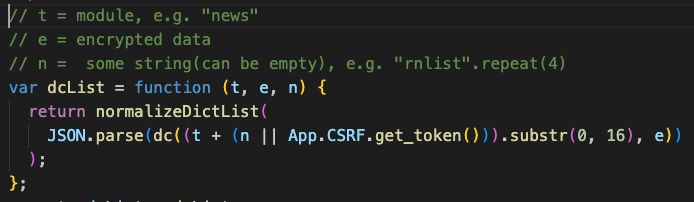
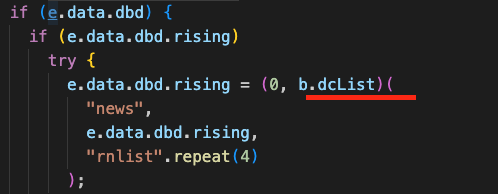
Revisiting the arguments passed to dc earlier, the first argument t(IV) is the first 16 characters of the module and some string or the CSRF token.
For posts API, t is news and n is empty.
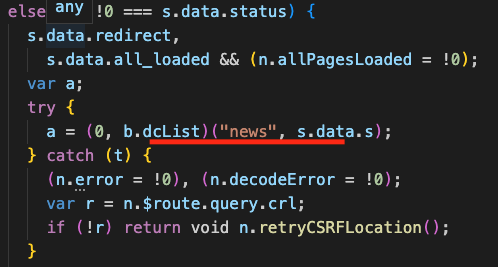
For dashboard API, t is also news while n is rnlistrnlistrnlistrnlist.
4. The final output
This is the final output of the posts and dashboard response after decrypting, decompressing and normalizing.
Try it out yourself
Here is a gist that you can use to try decoding the response yourself.
How to use
Create an
.envfile withCRYPTOPANIC_ENCRYPTION_KEYandCRYPTOPANIC_CSRF_TOKEN.Install the dependencies:
npm install dotenv pako crypto-jsRun
node decrypt.js [post|dashboard]